RIP is an old distance vector routing protocol. I wanted to give a quick over view of a potential problem when using authentication with RIP.
Below is the topology that we will be using.

RIPv2 has been enable on R1,R2, and R3. We have full reachability between our nodes. I have enabled plain text authentication on each link. Here is R2s output.
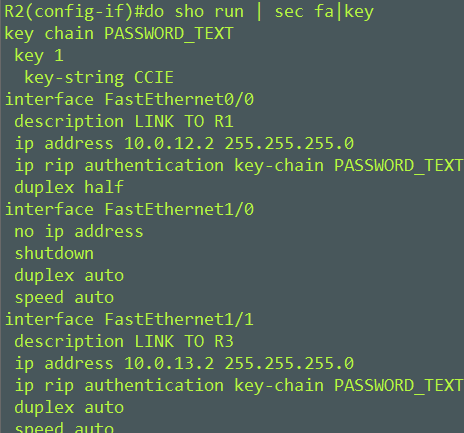
Key Chain = PASSWORD_TEXT
Key Number = 1
Key String = CCIE
I am going to setup a packet capture so we can view our RIP packets.

Notice that R2 10.0.12.2 is sending updates to the Multicast address for RIP 224.0.0.9. Authentication type: Simple password. Our password is CCIE. One thing in particular is that the Key identifier or our key number in our case 1 is arbitrary.
RIP plain text authentication doesn’t transmit the key identifier so you could have different key numbers on each of our routers. Say R1 = Key 1, R2 = Key 2, R3 = Key 3 and authentication would succeed as long as the password matches.
Lets switch our plain text authentication to use MD5 authentication between R1 and R2.

I created a new key chain and used MD5 authentication between R1 and R2. The link between R2 and R3 are still using plain text authentication.
Key Chain = PASSWORD_MD5
Key Number = 2
Key String = CCIE
I’ll setup a new packet capture between R1 and R2.

We have the same information as our last capture with two slight differences. We are using Authentication type: MD5 and now have a Key identifier field Key ID: 2
I’m going to change the Key ID on R1 to 1. Let’s see what happens when we have two different Key IDs.
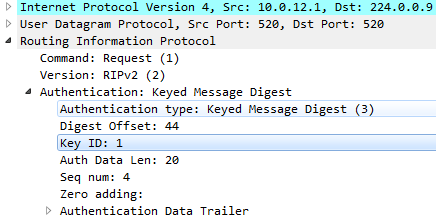
R1 is now using Key ID of 1. And below you see R1 ignoring RIP updates from R2 because authentication failed.

The point here is that when using RIP authentication with MD5 the Key identifier needs to match between routers. You see this in the packet capture, the Key identifier field is transmitted in the RIP payload. If Key ID differs, authentication will fail.
Mike

