I get the question a lot. What is a fabric? Most have an idea of what it is, but its a blurry idea. Fabric is a word that is being thrown around by many. It can be intimidating to ask, what exactly is a fabric. So today our goal is to provide an overview to the question. What is a fabric? I define it in the first section but get into some of the components throughout the post.
A fabric is a two layer construct. There is an underlay which is your physical make up of the network. Responsible for moving the packet. The overlay is the abstract service layer, it is responsible for things such as policies, segmentation, and mobility. Some overlay technologies that you may be aware of: CAPWAP, GRE, MPLS, DMVPN, OTV, ACI, LISP.
Overlays can come in two ways:
Layer 2 Overlays – Offers single subnet mobility within layer 2, extending L2 flooding.
Layer 3 Overlays – Offers IP mobility, Transports IP packets, contains failure domains.
So the new term for a LAN enabled fabric is ‘campus fabric’. However, its commonly shortened and referred to as a fabric or a fabric domain.
The campus fabric can be summarized as having
- LISP based Control-Pane
- VXLAN based Data-Plane
- Integrated Cisco TrustSec (policy plane)
Let’s pause to define some terms within the Campus Fabric. Don’t glaze over on me! Just be aware of these terms, no need to know them inside and out for this overview.
Control-Plane Node = LISP Map-Server : is a node in the fabric responsible for resolving EIDs to RLOCs
Edge Node = LISP Tunnel Router (xTR) : responsible for encapsulating the packet at the edge of the network and authenticating endpoints.
Border Node = LISP Proxy Tunnel Router (PxTR) : responsible for de-encapsulating the packet or encapsulating the packet when entering or leaving the fabric. Any traffic entering or leaving the fabric goes through this node. You NEED at least one of these.
Intermediate Node = Non-LISP IP forwarder : Imagine a 3-tier architecture; Access-Distro-Core, the Distro would be your intermediate nodes.
Fabric Domain = FD = LISP Process
Virtual Network = VN = LISP Instance = VRF : Maintains a separate Routing and switching instance for each virtual network
Endpoint ID Group = EIG = Segment = SGT : Each user of device is assigned to a unique Endpoint ID Group
Host Pool = Dynamic EID = VLAN + IP Subnet : Provides the basic IP constructs including Anycast Gateway.

LISP overview
Locator ID Separation Protocol – Now read that back sloooowly.. It’s self defining. LISP is separating IP(ID) from location(Locator).
LISP at it’s simplest form is nothing more than a mapping system but is a routing architecture, a control plane protocol and a data plane protocol. It separates Identity from a Location.
A devices IP (identity) is generally associated to a location of that device. If a device wants to roam to a new location the device needs a new IP (identity) for that location.
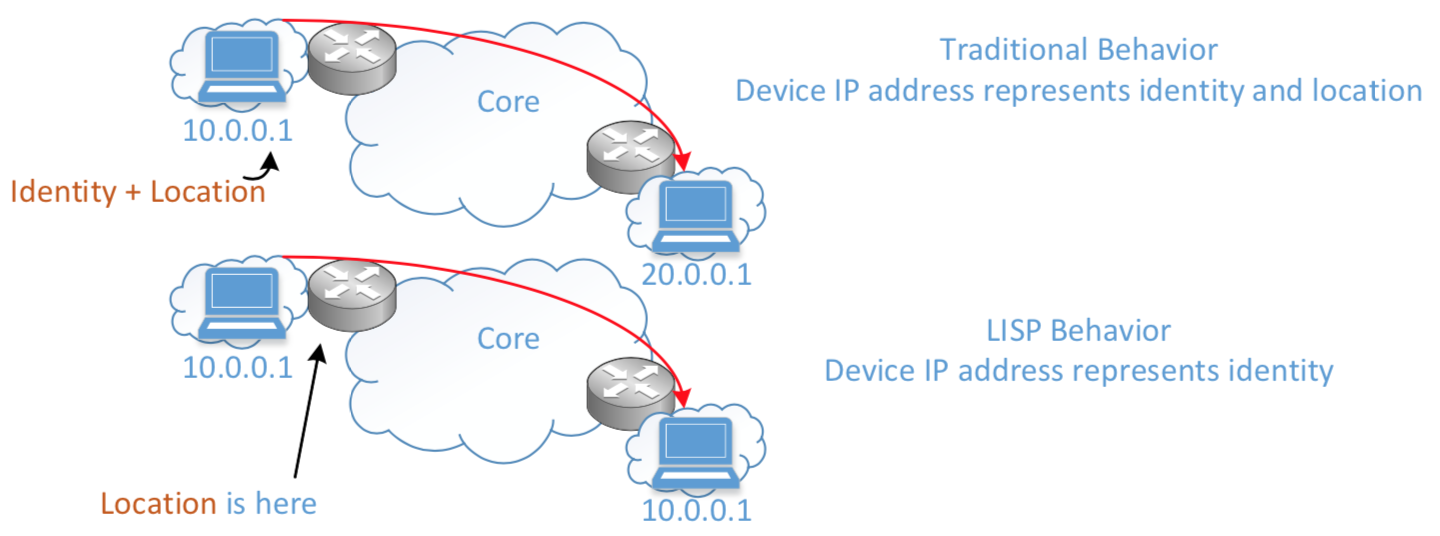
From a design perspective you can see how this can be helpful. This is just like when you roam between cell towers with your cell phone. Your location changes but your cell phone number (identity) does not.
LISP will assign End-point Identifiers or EID to hosts and will take on the role of acting as the devices identity. I don’t want to confuse you, EIDs do not replace a devices IP. EIDs are there to help RLOC map a device to a location.
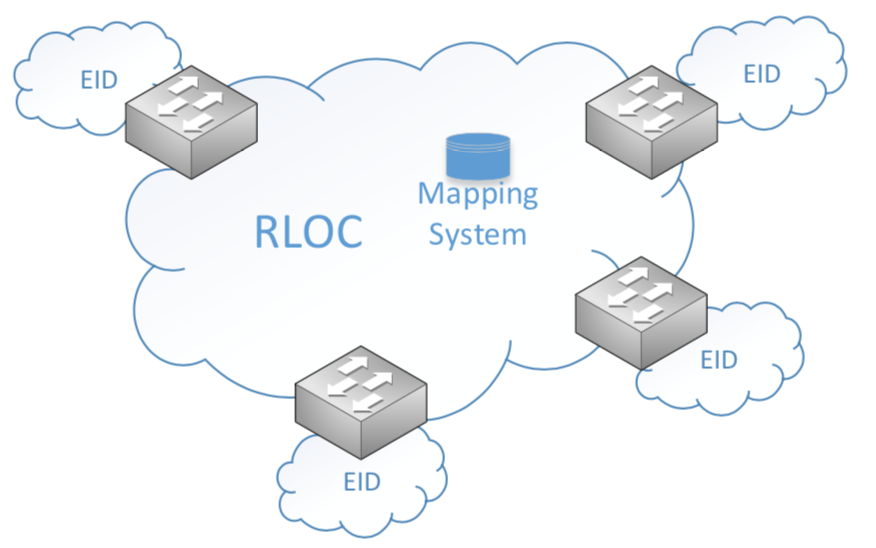
Routing locators or RLOCs map End-point Identifiers (EID) to a current location. The control plane node is responsible for doing this. RLOCs should be viewed as the Control plane protocol for LISP.
LISP mapping system can be analogous to a DNS resolution where DNS queries answer the “WHO IS” question and LISP resolution answered the “WHERE IS” question.
Why do I care about LISP? Because the fabric overlay is LISP enabled!
VXLAN Data-Plane Overview
VXLAN Encapsulation is used to carry L2 information. This is necessary because if we were to run LISP only, we would not be able to carry L2 information. LISP payload only supports L3 information. So, to achieve L2 and L3 capabilities, we run VXLAN.

What is Cisco TrustSec?
TrustSec (CTS) takes the complexity away from the static ACL and uses a tag based mechanism. So instead of creating enforcement on an IP you create enforcement around a tag which allows for mobility.
Lets wrap things up with a list of platforms that support campus fabric.
Fabric Edge Nodes
- Catalyst 9300 – IOS-XE 16.6.3+
- Catalyst 9400 – IOS-XE 16.6.3+
- Catalyst 3K – IOS-XE 16.6.3+
- Catalyst 4500 Sup8E+ – IOS-XE 3.9+
Fabric Border Nodes
- Catalyst 9500 – IOS-XE 16.6.3+
- Catalyst 3K
- Catalyst 6800 Sup2T/6T – IOS 15.4SY+
- ASR-1000-X/HX – IOS-XE 16.4+
- ISR4K – IOS-XE 16.4+
- Nexus 7700 w/ M3 cards – NX-OS 7.3.2+
Fabric Control Plane
- Catalyst 9500
- Catalyst 3K
- Catalyst 6800 Sup2T/6T
- ASR-1000-X/HX
- ISR4K
Lab it up! You only need three switches to test this out.
You can use the command ‘fabric auto’ which will automatically generate the necessary LISP and VXLAN configurations on the device so that the device can join the fabric.
For example:
Edge(config)# fabric auto
Edge(config-fabric-auto)# domain default
Edge(config-fabric-auto)# control-plan 7.7.7.7 auth-key key1
Edge(config-fabric-auto)# border 55.55.55.55I hope that this served as a basic overview to campus fabric. It is the behind the scenes magic of intent based networking.
Mike

