Welcome one, welcome all to the second blog. Today’s discussion will be on a bug that was found in a recent software upgrade to a 8510 wireless controller. Let’s begin.
If you are one to stay on the straight and narrow when it comes to downloading and installing Cisco software, then I applaud you. We have something in common. By the “straight and narrow” I mean, sticking to ‘Star’d’ releases. You know, the ones with the star just to the right of the software version? The Cisco’s “suggested release” based on software quality, stability and whatever else they deem star worthy. And the ones who are daring to test the waters of the non-star’d software versions. Eh, I guess I like you too.
It’s like dealing with the Salton sea when it comes to Cisco software releases. I mean come on! Feed the sea to much water and you begin to waste water. Feed the sea too little water, and the sea begins to evaporate leaving toxic sand behind. Before you know it, you’ve got asthma and not enough water to take a shower! Anyways I digress. It’s a double edge sword to say the least.
We have been using manufacturer installed certificate (MIC) for some time now. Basically just to contain unauthorized Cisco APs from joining our controllers. And up until now we have been utilizing the web interface to add the mac address of the AP to our AP policies. This changed after upgrading our controller to software version 8.0.133. After the upgrade, you can’t add mac address via the web interface. You get this nice little message.
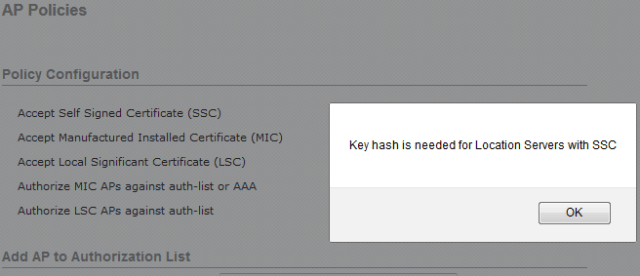
SSC isn’t checked! So what’s your issue man!
Through Cisco’s bug search tool this little guy came up.

The workaround was valid. It worked just fine through the cli.
In all, It really isn’t that big of a deal. It was something that I felt interesting enough to post about. The bug number is in the screen shot, but here it is if you missed it. CSCuz60224
Mike

